Of course! The java.security package is a fundamental and powerful part of the Java Development Kit (JDK). It provides the framework and classes for implementing security features, including cryptography, message digests, digital signatures, access control, and key management.
Let's break it down into a comprehensive guide.
What is java.security? (The Big Picture)
Think of java.security as the security toolkit for Java applications. It's not a single feature but a collection of building blocks that developers use to build secure systems. The primary goals it addresses are:
- Confidentiality: Ensuring that data can only be read by authorized parties. (Achieved with encryption).
- Integrity: Ensuring that data has not been altered in transit or at rest. (Achieved with message digests and digital signatures).
- Authentication: Verifying the identity of a user, system, or message. (Achieved with digital signatures and certificates).
- Authorization: Determining what an authenticated user or system is allowed to do. (Achieved with an Access Control List, ACL).
- Non-repudiation: Preventing a party from denying they sent a message or performed an action. (Achieved with digital signatures).
Core Components of java.security
Here are some of the most important classes and interfaces you'll find in the package.
A. java.security.MessageDigest
This is used to compute a "hash" or "message digest" of data. A hash is a fixed-size string of bytes that is a unique representation of the input data. Even a tiny change in the input data will produce a completely different hash.
-
Use Cases:
- Password Storage: You never store passwords in plain text. Instead, you store the hash of the password. When a user logs in, you hash their input and compare it to the stored hash.
- Data Integrity: You can hash a file before sending it and then hash it again after receiving it. If the hashes match, the file hasn't been corrupted.
- Blockchain/Cryptocurrencies: Hashing is the core technology behind blockchains.
-
Example: Hashing a String
import java.security.MessageDigest; import java.security.NoSuchAlgorithmException; import java.util.HexFormat; public class MessageDigestExample { public static void main(String[] args) { String data = "Hello, Security!"; try { // 1. Get a MessageDigest instance for SHA-256 MessageDigest md = MessageDigest.getInstance("SHA-256"); // 2. Compute the hash byte[] hashBytes = md.digest(data.getBytes()); // 3. Convert the byte array to a hexadecimal string HexFormat hex = HexFormat.of(); String hashString = hex.formatHex(hashBytes); System.out.println("Original Data: " + data); System.out.println("SHA-256 Hash: " + hashString); } catch (NoSuchAlgorithmException e) { System.err.println("SHA-256 algorithm not found."); e.printStackTrace(); } } }
B. java.security.SecureRandom
java.util.Random is predictable and not suitable for security-sensitive tasks like generating session IDs, cryptographic keys, or salts for passwords. SecureRandom is a cryptographically strong random number generator.
-
Use Cases:
 (图片来源网络,侵删)
(图片来源网络,侵删)- Generating salts for password hashing.
- Creating session tokens.
- Generating keys for encryption.
-
Example: Generating a Secure Random Number
import java.security.SecureRandom; public class SecureRandomExample { public static void main(String[] args) { // Create a SecureRandom instance SecureRandom secureRandom = new SecureRandom(); // Generate a random integer between 0 and 99 int randomInt = secureRandom.nextInt(100); System.out.println("Secure Random Integer: " + randomInt); // Generate a byte array for a cryptographic key byte[] key = new byte[16]; // 128-bit key secureRandom.nextBytes(key); HexFormat hex = HexFormat.of(); System.out.println("Secure Random Key: " + hex.formatHex(key)); } }
C. java.security.KeyPairGenerator and java.security.KeyPair
For asymmetric cryptography (like RSA), you need a pair of keys: a public key and a private key. The public key is used to encrypt data or verify signatures, while the private key is kept secret and is used to decrypt data or create signatures.
-
Use Cases:
- SSL/TLS: Securing web traffic (HTTPS).
- Digital Signatures: Signing software or documents.
- Key Exchange: Securely exchanging a shared secret over an insecure channel.
-
Example: Generating an RSA Key Pair
import java.security.KeyPair; import java.security.KeyPairGenerator; import java.security.NoSuchAlgorithmException; import java.security.interfaces.RSAPublicKey; import java.util.HexFormat; public class KeyPairGeneratorExample { public static void main(String[] args) { try { // 1. Get a KeyPairGenerator instance for RSA KeyPairGenerator keyPairGenerator = KeyPairGenerator.getInstance("RSA"); keyPairGenerator.initialize(2048); // Key size // 2. Generate the key pair KeyPair keyPair = keyPairGenerator.generateKeyPair(); // 3. Get the public and private keys java.security.PublicKey publicKey = keyPair.getPublic(); java.security.PrivateKey privateKey = keyPair.getPrivate(); System.out.println("Key Pair Generated Successfully!"); System.out.println("Algorithm: " + publicKey.getAlgorithm()); System.out.println("Public Key Format: " + publicKey.getFormat()); System.out.println("Public Key (Hex): " + HexFormat.of().formatHex(publicKey.getEncoded())); System.out.println("Private Key Format: " + privateKey.getFormat()); } catch (NoSuchAlgorithmException e) { System.err.println("RSA algorithm not found."); e.printStackTrace(); } } }
D. java.security.Signature and java.security.MessageDigest
This class is used for creating and verifying digital signatures. A digital signature proves the authenticity and integrity of a message.
-
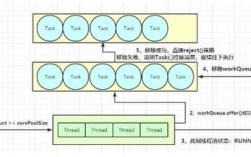
Process:
- Signing: The sender uses their private key and a
Signatureobject to create a signature for the message. - Verification: The receiver uses the sender's public key and the
Signatureobject to verify the signature against the received message.
- Signing: The sender uses their private key and a
-
Example: Signing and Verifying Data
import java.security.*; import java.util.HexFormat; public class SignatureExample { public static void main(String[] args) throws Exception { // 1. Generate a key pair (In a real app, you'd load these from a keystore) KeyPairGenerator keyPairGenerator = KeyPairGenerator.getInstance("RSA"); keyPairGenerator.initialize(2048); KeyPair keyPair = keyPairGenerator.generateKeyPair(); PrivateKey privateKey = keyPair.getPrivate(); PublicKey publicKey = keyPair.getPublic(); String data = "This data must be signed."; // 2. Sign the data Signature signature = Signature.getInstance("SHA256withRSA"); signature.initSign(privateKey); signature.update(data.getBytes()); byte[] digitalSignature = signature.sign(); System.out.println("Original Data: " + data); System.out.println("Digital Signature: " + HexFormat.of().formatHex(digitalSignature)); // 3. Verify the signature Signature verifier = Signature.getInstance("SHA256withRSA"); verifier.initVerify(publicKey); verifier.update(data.getBytes()); boolean isValid = verifier.verify(digitalSignature); System.out.println("Signature Verification: " + (isValid ? "SUCCESSFUL" : "FAILED")); } }
E. java.security.AccessController and java.security.Permission
This is the foundation for Java's security manager, which provides access control. It determines what code is allowed to do (e.g., read a file, connect to a network, access system properties).
-
How it works:
- Your code requests a
Permission(e.g.,java.io.FilePermission("test.txt", "read")). - The
AccessControllerchecks the "call stack" (the chain of methods that led to this request). - It consults a policy file (usually
java.policy) to see if the code at each level of the stack has been granted the requested permission. - If any code in the stack does not have the permission, a
SecurityExceptionis thrown.
- Your code requests a
-
Example: Checking a Permission
import java.io.FilePermission; import java.security.AccessController; import java.security.PrivilegedAction; public class AccessControllerExample { public static void main(String[] args) { // Define a permission to read the current directory FilePermission readPermission = new FilePermission(".", "read"); // Check if we have the permission try { AccessController.checkPermission(readPermission); System.out.println("Permission to read current directory GRANTED."); } catch (SecurityException e) { System.out.println("Permission DENIED: " + e.getMessage()); } // Example of privileged code String user = AccessController.doPrivileged((PrivilegedAction<String>) () -> System.getProperty("user.name")); System.out.println("Username (from privileged action): " + user); } }
Related but Crucial Packages
java.security doesn't work alone. It's often used with these packages:
javax.crypto: Provides the actual implementations for encryption and decryption algorithms (AES, DES, etc.). You usejava.securityto get the keys, andjavax.cryptoto perform the crypto operations.java.security.cert: Contains classes for handling X.509 certificates, which are used to bind public keys to identities (like websites or software publishers).java.security.KeyStore: Provides a secure way to store cryptographic keys and certificates. AKeyStoreis password-protected and can be saved to a file (e.g., a.jksor.p12file).
Best Practices
- Don't Roll Your Own Crypto: Always use well-established, vetted libraries from
java.security,javax.crypto, etc. Implementing your own encryption is extremely error-prone. - Use Strong Algorithms: Prefer modern algorithms like AES for encryption, SHA-256 or SHA-3 for hashing, and RSA or ECDSA for signatures. Avoid outdated ones like MD5 or SHA-1.
- Use
SecureRandomfor Everything Random: Never useMath.random()orjava.util.Randomfor security-sensitive randomness. - Use Salts When Hashing: When hashing passwords, always use a unique, random salt for each user to prevent rainbow table attacks.
- Store Keys Securely: Never hardcode keys in your source code. Use a
KeyStoreand manage it securely. - Principle of Least Privilege: Your application should only request the permissions it absolutely needs to function.