Of course! The term "dev random" in Python almost always refers to the two primary sources of random numbers provided by the operating system: /dev/random and /dev/urandom.
Let's break down what they are, how to use them in Python, and when to use each one.
The Short Answer: Use secrets for Security, random for General Use
For most developers, the best advice is:
- For security-sensitive applications (passwords, tokens, encryption keys): Use the
secretsmodule. It's designed for this and is the modern, easy-to-use standard. - For modeling, simulations, games, shuffling, etc. (non-security purposes): Use the
randommodule. It's faster and more convenient.
You don't need to interact with /dev/urandom directly in these cases, as Python's modules handle it for you.
The Low-Level Details: /dev/random and /dev/urandom
These are special files on Linux, macOS, and other Unix-like operating systems that act as interfaces to the kernel's random number generator.
/dev/urandom (Recommended for most cases)
- How it works: It uses an algorithm (like a Cryptographically Secure Pseudo-Random Number Generator or CSPRNG) to generate a stream of random-looking numbers. It's "pseudo-random" because it's deterministic, but the seed is based on a large amount of unpredictable entropy collected from the system (mouse movements, network packet timing, etc.).
- Key Characteristic: It is non-blocking. This means it will always return data immediately, even if the system's entropy pool is low. It will just keep generating numbers based on its current state.
- Use Case: Perfect for almost everything. It's fast, efficient, and considered cryptographically secure. It's the source Python's
secretsmodule and theos.urandom()function use by default.
/dev/random (Use with caution)
- How it works: It also collects entropy from the system but tries to be more "purely" random.
- Key Characteristic: It is blocking. If the kernel's entropy pool runs low (which can happen on a headless server or a VM that hasn't had much user interaction), a read from
/dev/randomwill pause and wait until enough new entropy is collected. This can cause your program to hang indefinitely. - Use Case: Only for very specific, high-stakes cryptographic applications where a theoretical weakness in a CSPRNG is a concern. For 99.9% of use cases,
/dev/urandomis sufficient and preferred.
How to Use Them in Python
Method 1: The Modern & Easy Way (secrets module)
This is the recommended approach for any security-related code. It was introduced in Python 3.6 to provide a simple, high-level interface for generating secure random numbers.
Key functions:
secrets.token_bytes(n): Generatesnrandom bytes.secrets.token_hex(n): Generatesnrandom bytes, represented as a hexadecimal string.secrets.token_urlsafe(n): Generatesnrandom bytes, represented as a URL-safe string.secrets.choice(sequence): Chooses a random element from a sequence.secrets.randbelow(n): Generates a secure random integer in the range[0, n).
Example: Generating a secure API key
import secrets
# Generate a 32-character URL-safe token (good for API keys or session IDs)
api_key = secrets.token_urlsafe(32)
print(f"Secure API Key: {api_key}")
# Generate a 16-byte random number, represented as a hex string
session_token = secrets.token_hex(16)
print(f"Session Token: {session_token}")
# Securely pick a random item from a list
colors = ['red', 'green', 'blue', 'yellow', 'purple']
secure_color = secrets.choice(colors)
print(f"Your lucky color is: {secure_color}")
Method 2: The Standard Library Way (random and os modules)
A. The os.urandom() function
This is the low-level function that reads directly from /dev/urandom. It's the foundation that secrets and random.SystemRandom are built upon. It returns bytes.
import os
# Get 16 random bytes from /dev/urandom
random_bytes = os.urandom(16)
print(f"Random bytes from os.urandom: {random_bytes}")
# You can convert these bytes to other formats
# To a hex string
hex_string = random_bytes.hex()
print(f"As a hex string: {hex_string}")
# To an integer
random_integer = int.from_bytes(random_bytes, 'big')
print(f"As a large integer: {random_integer}")
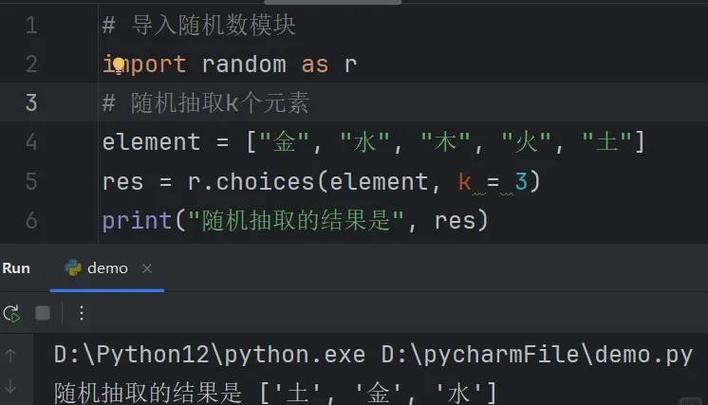
B. The random module (for non-security purposes)
The standard random module is NOT suitable for security. It's a pseudo-random number generator (PRNG) that is predictable. However, you can make it use the secure os.urandom() as its source.
Example 1: Using the standard random module (INSECURE)
import random
# This is predictable and should NOT be used for passwords or tokens
insecure_token = random.getrandbits(128) # Gets a 128-bit random number
print(f"Insecure token: {insecure_token}")
Example 2: Using random.SystemRandom (SECURE)
This class uses os.urandom() as its source, making it cryptographically secure. It's an alternative to the secrets module.
import random
# Create a SystemRandom instance
secure_random = random.SystemRandom()
# Now you can use all the standard random functions, but they are secure
# Generate a secure random integer between 1 and 100
secure_number = secure_random.randint(1, 100)
print(f"Secure random number: {secure_number}")
# Securely shuffle a list
cards = ['Ace', 'King', 'Queen', 'Jack']
secure_random.shuffle(cards)
print(f"Shuffled cards: {cards}")
Summary Table: Which to Use?
| Goal | Recommended Module | Why? |
|---|---|---|
| Generate passwords, API keys, tokens | secrets |
Purpose-built for security. Simple, readable, and uses /dev/urandom under the hood. |
| Generate encryption keys | secrets |
Cryptographically secure. Ensures keys are unpredictable. |
| Simulate dice rolls, card games | random |
Fast and convenient. Not for security, perfect for modeling and games. |
| Randomly pick an item from a list | random (general) |
Fast and easy. |
| Randomly pick an item for security | secrets.choice() |
Ensures the choice is not predictable. |
| Low-level access to random bytes | os.urandom() |
Directly reads from /dev/urandom. Use when you need raw bytes for custom cryptographic operations. |
Final Recommendation
- If you are writing any code related to security, authentication, or cryptography, use the
secretsmodule. It's the right tool for the job and prevents common mistakes. - If you are writing a game, a simulation, or need to shuffle data for non-security reasons, use the
randommodule. - You will almost never need to open the
/dev/randomor/dev/urandomfiles manually. Python's built-in modules provide a much safer and more convenient interface.