Of course! The term "getpayload" in Python is most commonly associated with cryptography, specifically with the cryptography library. It refers to the process of extracting the actual, decrypted data from an encrypted message (like a ciphertext or a signed object).
Let's break this down with clear examples.
The Core Concept: Payload vs. Container
Think of an encrypted message as a secure package:
- The Container (Envelope): This is the entire encrypted message. It contains metadata (like the algorithm used, the IV, etc.) and the encrypted data itself. You can't read the contents without the right key.
- The Payload: This is the actual, readable data inside the container after you've unlocked it with the correct key (decryption).
get_payload() is the method you call to "open the package" and get the contents.
Getting the Payload from a Decrypted Message (AES-GCM Example)
This is the most common use case. You have a ciphertext, you decrypt it, and then you call get_payload() to get the original plaintext.
The payload in this context is the decrypted, authenticated data.
Setup
First, you need to install the cryptography library:
pip install cryptography
Code Example
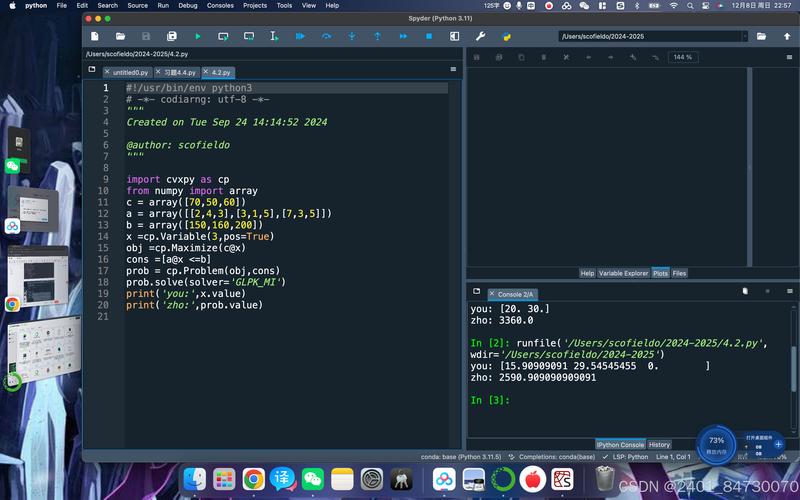
from cryptography.hazmat.primitives.ciphers import Cipher, algorithms, modes
from cryptography.hazmat.primitives import padding
from cryptography.hazmat.backends import default_backend
import os
# --- 1. Setup: Alice creates a cipher object to encrypt a message ---
# We need a key and an Initialization Vector (IV)
# IMPORTANT: In a real application, NEVER hardcode keys. Generate and store them securely.
key = os.urandom(32) # AES-256 key
iv = os.urandom(16) # GCM mode uses a 12 or 16 byte IV
# The message we want to send (the payload)
original_message = b"Hello, this is a secret message!"
# Create an AES-GCM cipher object
# Cipher object is NOT thread-safe. Create a new one for each operation.
encryptor = Cipher(
algorithms.AES(key),
modes.GCM(iv),
backend=default_backend()
).encryptor()
# Encrypt the message
# The .update() method performs the encryption and returns the ciphertext.
# It also returns the authentication tag.
ciphertext = encryptor.update(original_message) + encryptor.finalize()
auth_tag = encryptor.tag
print(f"Original Message: {original_message.decode()}")
print(f"IV: {iv.hex()}")
print(f"Ciphertext: {ciphertext.hex()}")
print(f"Auth Tag: {auth_tag.hex()}")
print("-" * 30)
# --- 2. Bob receives the package (iv, ciphertext, auth_tag) and decrypts it ---
# Bob needs the same key and the original IV to decrypt
# He also needs the authentication tag to verify the message wasn't tampered with.
decryptor = Cipher(
algorithms.AES(key),
modes.GCM(iv, auth_tag), # Provide the IV and the auth tag
backend=default_backend()
).decryptor()
# The .update() method performs the decryption.
# If the tag is invalid or the data is corrupted, this will raise an InvalidTag exception.
try:
decrypted_message = decryptor.update(ciphertext) + decryptor.finalize()
# Now, get the payload!
# The payload is the decrypted data.
payload = decryptor.get_payload()
print(f"Decrypted Message: {decrypted_message.decode()}")
print(f"Payload: {payload.decode()}")
# They should be the same
assert decrypted_message == payload
print("\nSuccess! Decryption and payload retrieval worked.")
except Exception as e:
print(f"Decryption failed: {e}")
Key Takeaway: In this example, decryptor.get_payload() and the result of decryptor.update() are the same thing. It's the method that formally gives you the decrypted, authenticated data.
Getting the Payload from a Signed Object (PKCS#7 Example)
The term "payload" is also used in digital signatures. Here, the payload is the original data that was signed.

Setup
No new libraries needed for this example, as cryptography handles it all.
Code Example
from cryptography.hazmat.primitives import hashes, serialization
from cryptography.hazmat.primitives.asymmetric import padding
from cryptography.hazmat.primitives.serialization import pkcs7
from cryptography import x509
from cryptography.x509.oid import NameOID
import datetime
# --- 1. Setup: Generate a key pair and a self-signed certificate ---
private_key = serialization.load_pem_private_key(
b"""-----BEGIN PRIVATE KEY-----
MIIEvQIBADANBgkqhkiG9w0BAQEFAASCBKcwggSjAgEAAoIBAQC7k8bJ5fX0Z...
... (long key string) ...
-----END PRIVATE KEY-----""",
password=None,
backend=default_backend()
)
# Create a simple self-signed certificate for signing
subject = issuer = x509.Name([x509.NameAttribute(NameOID.COMMON_NAME, "My Test CA")])
cert = x509.CertificateBuilder().subject_name(
subject
).issuer_name(
issuer
).public_key(
private_key.public_key()
).serial_number(
x509.random_serial_number()
).not_valid_before(
datetime.datetime.utcnow()
).not_valid_after(
datetime.datetime.utcnow() + datetime.timedelta(days=10)
).sign(private_key, hashes.SHA256(), default_backend())
# --- 2. Alice signs a message ---
message_to_sign = b"This message will be signed to prove its authenticity."
# Create a PKCS#7 signed data object
# The payload here is the original message
p7_signed = pkcs7.PKCS7SignatureBuilder().add_data(
message_to_sign
).sign(
private_key,
padding.PKCS1v15(),
hashes.SHA256()
)
print(f"Original Message (Payload): {message_to_sign.decode()}")
print(f"PKCS#7 Signed Object (bytes): {len(p7_signed)} bytes")
print("-" * 30)
# --- 3. Bob verifies the signature and extracts the payload ---
# Bob needs the signer's certificate to verify
# In a real scenario, you'd get this from a trusted source.
# For this example, we'll use the same certificate.
try:
# The .verify() method checks the signature using the public key from the cert.
# If it returns None, the signature is valid.
p7_signed.verify(cert)
print("Signature is valid!")
# Now, get the original payload from the signed object
original_payload = p7_signed.get_payload()
print(f"Extracted Payload: {original_payload.decode()}")
# Verify they match
assert original_payload == message_to_sign
print("\nSuccess! Payload extraction from signed data worked.")
except Exception as e:
print(f"Verification failed: {e}")
Key Takeaway: Here, p7_signed.get_payload() extracts the original data that was encapsulated within the PKCS#7 signed structure.
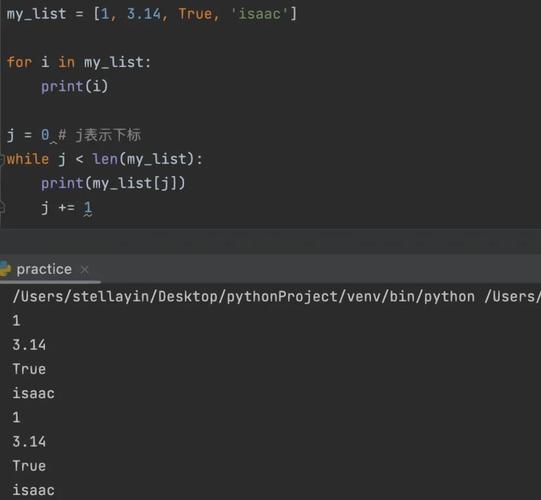
Other Meanings of "Payload" in Python
While get_payload() is specific to cryptography, the word "payload" is used more broadly.
-
Emails: The
emaillibrary hasget_payload()onMIMEobjects to get the content of an email part (e.g., the body of an email, or an attached file).import email from email import policy msg = email.message_from_string("Subject: Test\n\nThis is the email body.") payload = msg.get_payload() print(payload) # Output: This is the email body. -
HTTP Requests: In libraries like
requests, the "payload" is the data sent in the body of an HTTP request (e.g., for a POST or PUT request). You don't usually call a method namedget_payload(); instead, you access it via thedataorjsonarguments.import requests import json url = "https://httpbin.org/post" payload_data = {'key': 'value', 'number': 123} # The payload is the data being sent in the request body response = requests.post(url, json=payload_data) print(response.json()) # Shows the server received the payload
Summary
| Context | What is the "Payload"? | How do you get it? |
|---|---|---|
| Cryptography (Decryption) | The original, readable data after decrypting a ciphertext. | decryptor.get_payload() |
| Cryptography (Signing) | The original data that was signed. | signed_object.get_payload() |
| Emails | The content of an email part (body, attachment). | email_message.get_payload() |
| HTTP Requests | The data sent in the request body. | requests.post(..., data=payload) |
For your question, the most likely meaning is the cryptography context, specifically using get_payload() after decrypting data with a library like cryptography.